A rare and serious vulnerability in Apple’s iOS operating system has been discovered by researchers at the University of Toronto’s Citizen Lab, which today published a report detailing its findings. It is the first known remote iOS vulnerability of its kind. Disturbingly, the company behind malware designed to exploit the security flaw may have also helped target an investigative journalist in Mexico in 2015, Citizen Lab said.
The report illustrates the growing threat that commercially-available malware poses to journalists around the world. Apple’s iOS-based devices are generally considered by experts to be among the safest options for journalists in the field.
That such an attack was possible is “mind-boggling,” Citizen Lab Senior Research Fellow Bill Marczak told CPJ. “I’ve never heard of this before.”
Apple issued a security update today in iOS 9.3.5 to address the vulnerability. An attacker could use the security flaw to remotely commandeer a target device running 9.3.4 or below, so CPJ strongly urges journalists who own iOS devices — such as iPhones and iPads — to install the update immediately. (CPJ always recommends that journalists install security updates as soon as they become available, and enable automatic security updates on devices for which it is an option.)
The surprising vulnerability discovered in iOS should not, however, prompt journalists to give up on their Apple devices, whose numerous factors to protect users’ privacy and security include robust encryption by default–unlike many phones running versions of the Android operating system.
“If this had happened on an Android device, who knows how long we’d have to wait until a patch was available,” Eva Galperin, global policy analyst at Electronic Frontier Foundation, told CPJ via Twitter.
While iOS is developed, maintained, and updated by Apple, Android is an open source platform developed by Google but modified by phone manufacturers to suit their needs. Android’s fragmentation means that Google has little control over when devices receive security updates.
Citizen Lab researchers Marczak and John Scott-Railton wrote that they discovered the iOS vulnerability after Ahmed Mansoor, an award-winning human rights defender in the United Arab Emirates, forwarded messages containing suspicious links he began receiving two weeks ago. To assess whether the links led to malware designed to take over Mansoor’s iPhone 6, Marczak opened one of them using a freshly-wiped iPhone running a recent version of iOS. To the naked eye, what happened next was subtle, Marczak told CPJ. But by monitoring the phone’s activity on the network, he was able to witness an efficient cascade of actions designed to compromise the phone entirely.
“It was very deliberate and well thought out,” Marczak told CPJ.
According to the Citizen Lab report, technical details of the attack indicate the malware was created by the Israeli surveillance firm NSO Group.
Zamir Dahbash, an NSO Group spokesman, told The New York Times that the company “sells only to authorized governmental agencies, and fully complies with strict export control laws and regulations.” He would not say if the software is used by government agencies in the U.A.E. or Mexico, but said, “The products may only be used for the prevention and investigation of crimes,” the Times reported.
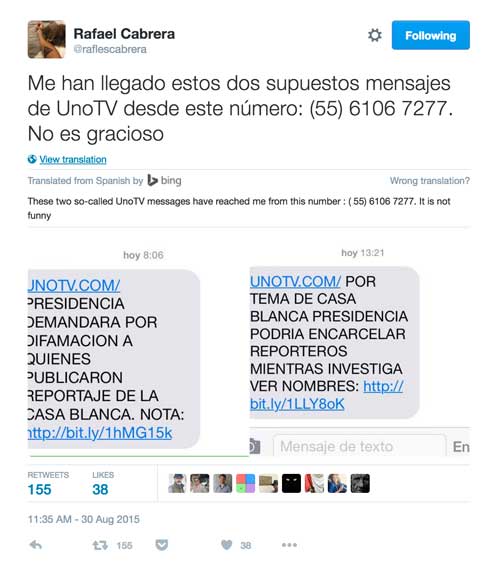
By tracing the hyperlinks sent to Mansoor and comparing the results to their prior research, Marczak and Scott-Railton were able to connect the suspected NSO malware delivery servers to hyperlinks contained in text messages sent to Rafael Cabrera, a Mexican investigative journalist who in 2014 reported on an alleged conflict of interest involving the president and first lady of Mexico. Two of the links sent to Cabrera were disguised in messages appearing to originate with another news organization, UNO TV, according to screenshots of the messages Cabrera tweeted on August 30, 2015. The messages purported to warn Cabrera about possible defamation claims and even prosecutions of journalists connected with Cabrera’s reporting. A Director a UNO TV, Luis Vázquez Fabris, responded to Cabrera’s tweet to deny his organization had sent the messages.
CPJ was not immediately able to reach Cabrera by phone.
Neither Mansoor nor Cabrera appear to have been ultimately hacked, showing that journalists who are vigilant and avoid falling for dirty tricks can avoid malware. This is important because although today’s update from Apple blocks the exploit discovered by Citizen Lab, it is possible that other vulnerabilities exist.
“Building secure software is a highly challenging task, even for a world-class team such as Apple’s,” Riana Pfefferkorn, Cryptography Fellow at the Stanford Center for Internet and Society, told CPJ via Twitter. Government attempts to undermine security for law enforcement purposes only make the problem worse., she said. “Governments that are determined to go to such great lengths to target journalists and human rights activists like Ahmed Mansoor would welcome purpose-built backdoors with open arms. Software security is crucial to the future of journalism, and the laws of every country should reflect that.”
Journalists can learn how to better protect themselves by downloading CPJ’s Journalist Security Guide, which contains a dedicated section on technology security best practices.
If you suspect you have been targeted in connection with your work, please contact CPJ. The safest way to do so is via SecureDrop, which you can access via the Tor browser at 2x2hb5ykeu4qlxqe.onion.
Alexandra Ellerbeck, research associate in CPJ’s Americas program, and Tom Lowenthal, CPJ’s staff technologist, contributed reporting.
