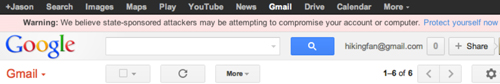
Some journalists continue to receive the warning from Google about state-sponsored attacks that we mentioned last week. The message appears on top of logged-in services like Gmail. Occasionally it will disappear for a few hours and then reappear, but there is no way to remove it.
The warning can be disturbing, especially as the company does not provide much information, such as why it suspects such an origin for a hacking attack. Instead, it gives a link to its support pages explaining some general ways to increase the security of your Google account.
Faced with the news that an entire nation-state is apparently intent on hacking your computer, taking care to not open strange email attachments and watching a video about strong passwords may hardly seem sufficient.
What follows is a little more explanation, based on CPJ’s experiences with journalist information security, about what Google may be seeing, and how you might defend yourself.
What does a state-sponsored attack look like?
In Syria, citizen reporters get sent fake video messages on Skype with malicious software attached. Hong Kong websites used by reporters are hacked and dangerous payloads inserted so that they might be downloaded by unsuspecting visitors.
These attacks may be orchestrated by states, but the techniques are similar to those used by petty Internet criminals, who attempt to take control of Internet users’ computers via mass fraudulent emails (“phishing”) or constructing fake websites masquerading as legitimate.
The difference between suspected state-sponsored cybercrime and this constant background cybercrime is not the sophistication or success of the attacks, but the targets. Some attacks are aimed at a small list of notable users–say, Tibetan activists, foreign correspondents in Shanghai, and Western diplomats; Iranian government officials and nuclear equipment engineers–rather than the scattergun lists of millions that most commercial cybercrime exploit.
Google’s warnings appear to be based on their systems for detecting run-of-the-mill cyberattacks. The company says, “…our detailed analysis–as well as victim reports–strongly suggest the involvement of states or groups that are state-sponsored” and warns users against fake websites and attachments in emails. Given this, our best guess is that Google is deducing a state attack partly because of who is being targeted.
While the targeting is narrower than with phishing mails that are spammed to millions of addresses, these state-sponsored attacks are still being launched against hundreds or thousands rather than dozens of users. We’ve heard many reports of these warning signs. If your Google account is flagged, it’s probably because you’ve ended up on some fairly large target list.
Internet self-defense
In terms of defending yourself, it doesn’t really matter whether these attacks are state-sponsored or not. The tactics of the attacker remain the same: repeated attempts to guess passwords and psychological tricks to fool users into entering their passwords on fake websites or opening dangerous attachments.
Everyday computer security advice, such as Google’s, is just as valid against a group of opportunistic state-led hackers aiming at independent journalists or activists as it is against a group targeting the average consumer.
One of the best ways you can defend against all of these attacks is to choose a stronger password. Another is to regularly update your computers’ software to protect against security flaws. Finally, a specific technique against these attacks on Google’s services is to use two-step verification. Two step verification means that when you log in with your password, Google will double-check to ensure that you are who you say you are. It will text you an additional password to enter, or ask you for a number that only you know, produced by a local app on your mobile phone. Google’s info page on the attacks encourages all of these strategies.
The future
State-sponsored attacks can also be indicated by the unique resources exploited by the attacker. In the case of the “Flame” malware, which is suspected of being developed by a major Western power, the malicious software is unusually complex, and includes techniques that appear to have come from detailed mathematical research. In Iran and Tunisia, the governments used their control of the local telecommunications systems in attacks against domestic users’ privacy.
In these cases, governments are not just using the strategies of petty Internet criminals. They are marshaling their unique state-owned resources against individuals.
There’s no indication that Google is detecting such heavyweight attacks; its advice would be very different if it were. But those who have received its warning message may face such attacks in the future.
If and when this happens, standard consumer advice may not be enough. To give a concrete example: hackers have already bypassed two-factor authentication systems by simultaneously obtaining the standard password, then taking control of the victim’s phone line as well. State-sponsored attackers with access to the mobile phone network could, of course, do the same.
Journalists we spoke to were already aware of these risks. Some who had received Google’s warning were concerned that Google’s two-factor authentication required them to give Google their mobile phone number online, and refused to do so. (While Google does oblige you to enter your phone number in their two-factor setup procedure, you can remove the number after setup, if you set your smartphone to generate its own passwords locally.)
These reporters’ caution is understandable. As we say in CPJ’s Journalist Security Guide, your best defense is your professional knowledge of potential attackers.
Google’s general warning about state attacks is a useful clue as to who may be interested in you, and for now, the company’s security advice is good. But it’s always worth thinking about the specifics of your own situation, and taking extra precautions.
While Google and other “cloud” services would never instruct you to do so, you may wish to delete confidential data held in online accounts, or even close down a targeted account entirely. You also might want to compartmentalize data by keeping it offline, or use separate accounts on separate computers. Think about how the attacker might have obtained enough information to target your account. Do they just know your email address? Have your colleagues been similarly targeted? Discuss with others what you’ve learned, and share advice.
Above all, don’t feel too singled out. There are a lot of people seeing Google’s warning. If you haven’t already considered that you are attracting the attention of the local authorities, it’s a useful new indication. But most journalists already know they are on a government list. Google’s warning should remind us to do online what good journalists have always done: be careful about what you say, and what information you keep or hand out to third parties–including services like Google.
(Thanks to Internews and Google for assistance with this article.)