Cyberattackers used services of technology companies based in the U.S. and U.K. to target media sites from Somalia, Kosovo, and Turkmenistan, Qurium, a nonprofit hosting the sites, said Tuesday. Earlier this month, CPJ reported on how cyberattackers used a Nebraska company, RayoByte, in attempts to knock those same media sites offline, as well as at least three others in Nigeria, Kyrgyzstan, and the Philippines.
The findings provide new insight into how private companies are being used by malicious actors to try to suppress online reporting around the globe.
In its new report, Qurium said services from U.S. companies phoenixNAP and Aliat Data and U.K. company IPXO had been used to conduct cyberattacks against media websites during August of this year. Those sites belong to the Somali Journalists Syndicate press freedom group, Turkmen.news, an exile-run site covering Turkmenistan, and Nacionale, in Kosovo. All three outlets have previously faced censorship and intimidation efforts, including the arrest of employees, physical violence, and online harassment.
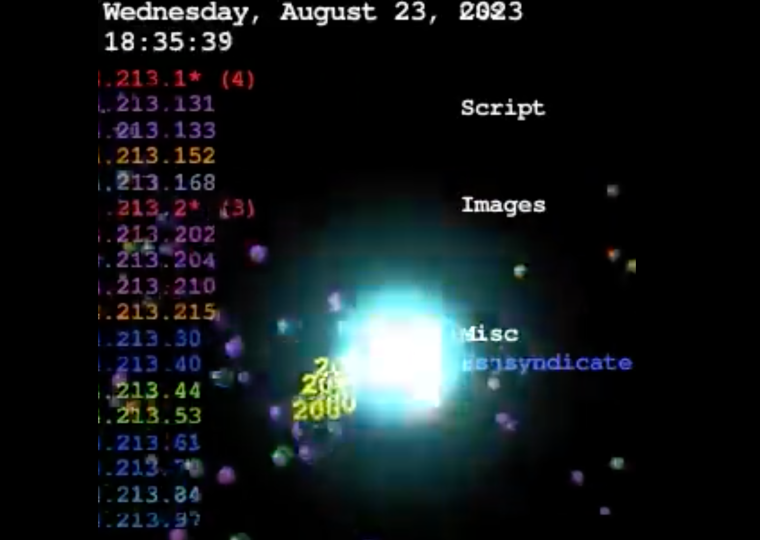
In August, the three media outlets were hit with distributed denial-of-service (DDoS) attacks, when internet traffic is deliberately directed at a website in order to knock it offline. The traffic used in the attacks came from Internet Protocol (IP) addresses, unique numbers assigned to internet-connected devices.
While it remains unknown who ordered the attacks, Qurium technical director Tord Lundström told CPJ that his group was able to map out how the services of U.K. and U.S. companies were used to try to take the media outlets down. Aliat Data leased thousands of IPs from IPXO; those IPs were then routed through servers at phoenixNAP’s datacenter in Ashburn, Virginia, in order to hit the sites. Qurium was able to defend against the attacks, so the media sites remained accessible.
The companies respond
Qurium has been in contact with all three companies to alert them to the DDoS attacks. Aliat Data, the company that operated the IPs when the incidents took place, said that it didn’t conduct the cyberattacks. An email from Gustavo Colombini, who works on infrastructure at Aliat Data, said that the company doesn’t “perform these types of attacks.” Colombini blamed the attacks on “security issues that could lead to these IPs being abused by external actors,” and said Aliat Data was fixing the issues.
“[W]e were basically serving hand-picked customers,” Colombini wrote to Qurium. The attackers could not be identified, Colombini said, because Aliat Data “never had in place a good monitoring mechanism.” Colombini also said: “No customer of ours was likely launching any type of attack.”
In response to CPJ’s email requesting an interview, Colombini repeated that Aliat Data did not conduct the attacks. “[A] key piece of our infrastructure was abused by external forces and the issue was solved as soon as we diagnosed it. We are working to improve our security mechanisms and it includes better monitoring,” Colombini wrote.
IPXO, the company that leased the IPs to Aliat Data, said that its client provides services for “web-scraping,” a common research method. After Qurium alerted the company to the attacks, it “suspended” the client – which it did not name – while an “incident investigation” was ongoing. The company provided no further details of the suspension.
phoenixNAP, whose servers were used to direct the traffic in the attack, told Qurium that the “client responsible” had informed the company that “all of this has been caused by misconfiguration from one of his [the client’s] customers.” phoenixNAP also didn’t name the client, saying “[u]nless it is requested by law enforcement, we can not disclose any information about our clients as it would be considered as a breach of contract…” It also said “we do not tolerate network abuse.”
As of mid-September, online databases showed Aliat Data still operated the IPs from phoenixNAP’s servers.
CPJ emailed IPXO and phoenixNAP requesting interviews, but neither responded.
The companies’ identities
Both IPXO and phoenixNAP offer a variety of products and services on their websites. IPXO, based in London, bills itself as “The World’s First IP Marketplace” and sells access to IP addresses, including short term leases. Arizona-based phoenixNAP has 15 data centers around the world, and in 2012 acquired another computing company called Secured Servers. It sells information technology and computing services, including internet traffic routing.
Aliat Data’s website, on the other hand, offers little information about its business, but advertises “proxy” and “data scraping” services, which may be used to facilitate less clearly traceable internet traffic and conduct bulk information collection online. Its site lists a Las Vegas address for Aliat LLC, but Wyoming state records show a company named Aliat LLC registered through the firm Registered Agents Inc.
A customer service representative at Registered Agents Inc. told CPJ by phone that it is the registered agent for thousands of companies and could not provide any “significant insights into [Aliat LLC’s] leadership.” The representative said Registered Agents Inc. receives and passes along state mail and lawsuits to its companies, and could share no information about those companies without permission.
Reporting last year by the International Consortium of Investigative Journalists and the Washington Post detailed how business entities with little oversight may be used by alleged criminals to avoid scrutiny. They named Registered Agents Inc. in their coverage of the issues. The Registered Agents Inc. representative was not aware of previous reporting about the company.
Defense against the attacks
Analysis of the IPs used to target the sites revealed a pattern that made defending against them more difficult. Qurium found that IPs used in the attacks had been routed through various locations over the years and months prior, initially obscuring the fact that it came from phoenixNAP’s Ashburn, Virginia, data center. This made it harder for Qurium to guard the websites from the malicious traffic, Lundström said.
“You have no patterns, you just have noise everywhere. You see different countries, you don’t know if these are real [news] readers,” he said.
The IPs leased by Aliat Data and involved in the attacks have not hit the three sites since late August, Lundström told CPJ. But questions of accountability – and the identities of those behind these attacks on independent media sites – remain. “That’s the power of DDoS,” he said. “It never comes with a signature.”